Three-Quarters of Vulnerabilities Used in Ransomware Attacks Were Discovered Before 2020

Despite a lot of focus on phishing and remote access as initial access vectors, new data shows the use of vulnerabilities is not only on the rise, but simply isn’t being properly addressed.
The report, Ransomware 2023, put out jointly by cybersecurity vendors Securin, CybersecurityWorks, Ivanti, and Cyware, highlights the use of vulnerabilities within ransomware attacks. According to the report, vulnerabilities are alive and well in modern attacks:
- 81 vulnerabilities exist that provide attackers with end-to-end access – from initial access to exfiltration – have been identified within popular operating systems, databases, storage, virtualization and firewall solutions.
- 76% of vulnerabilities exploited by ransomware are old – really old. Many of them were discovered between 2010 and 2019!
- The number of vulnerabilities associated with ransomware attacks has grown 19% with a total count of 344 since 2019
At present, according to the report, there are a total of 11,778 weaponized vulnerabilities documented; this reaches far beyond just ransomware and represents all known vulnerabilities including those that have been addressed with updates.
While the 81 vulnerabilities provide threat actors with relatively complete access for an attack, not every organization has the required platform to take advantage of one of these vulnerabilities. The result is many vulnerabilities only provide initial access, requiring that threat actors return to more traditional actions that include the need to compromise credentials – something that generally accomplished using internal spear phishing.
So, even as I conclude this article about the threat of vulnerabilities, don’t forget they only play a role in most cyberattacks and that phishing continues to be the most leveraged attack method – demonstrating the need for Security Awareness Training to ensure when internally- or externally-based phishing attacks occur, users are certain to spot these malicious emails for their true purpose and never engage to enable the attacker.
Free Ransomware Simulator Tool
Threat actors are constantly coming out with new strains to evade detection. Is your network effective in blocking all of them when employees fall for social engineering attacks?
KnowBe4’s “RanSim” gives you a quick look at the effectiveness of your existing network protection. RanSim will simulate 22 ransomware infection scenarios and 1 cryptomining infection scenario and show you if a workstation is vulnerable.
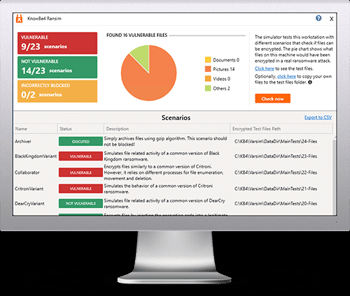
Here’s how it works:
- 100% harmless simulation of real ransomware and cryptomining infections
- Does not use any of your own files
- Tests 23 types of infection scenarios
- Just download the install and run it
- Results in a few minutes!
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

